Azure Automation and Using Hybrid workers runbook on vSphere
During the day I have been digging into the Microsoft Operations Management Suite which is a collection of cloud services that you can get for a quite reasonable price.
The different services included is Log Analytics, Security, Automation, Availability.
I have registered my on premise Windows Servers in the log analyzer and started uploading logs getting a nice overview with several out of the box solutions that will give you a heads up on areas in your environment that needs attention…
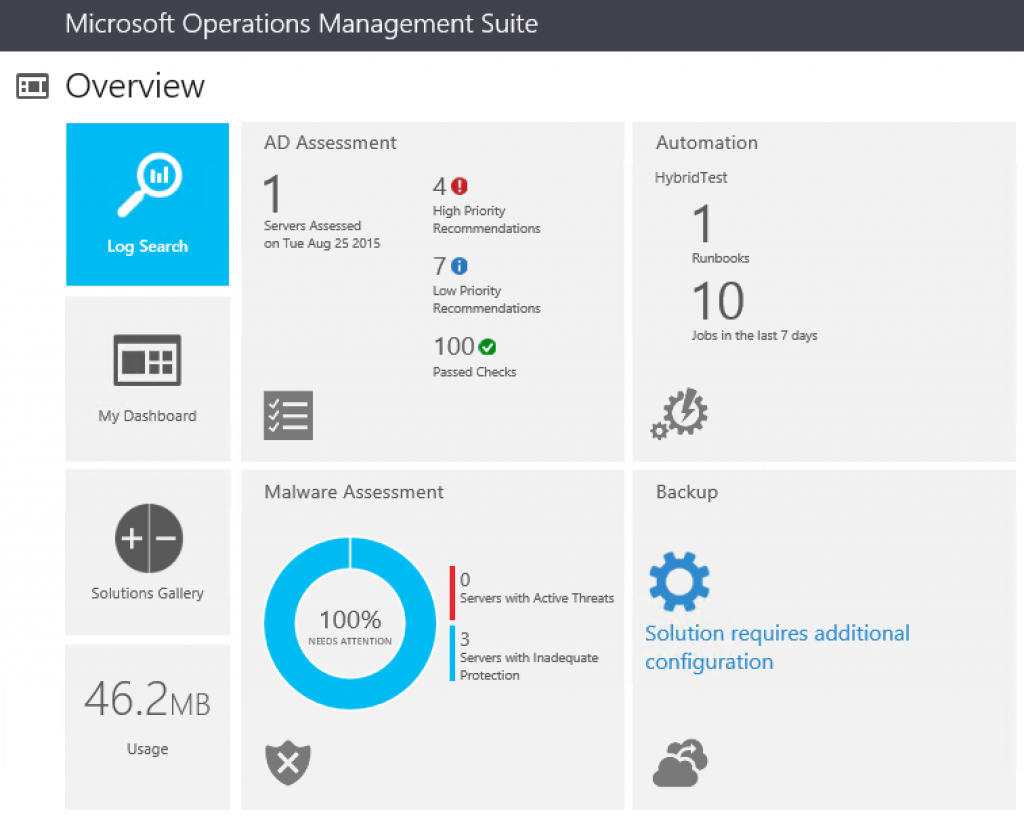
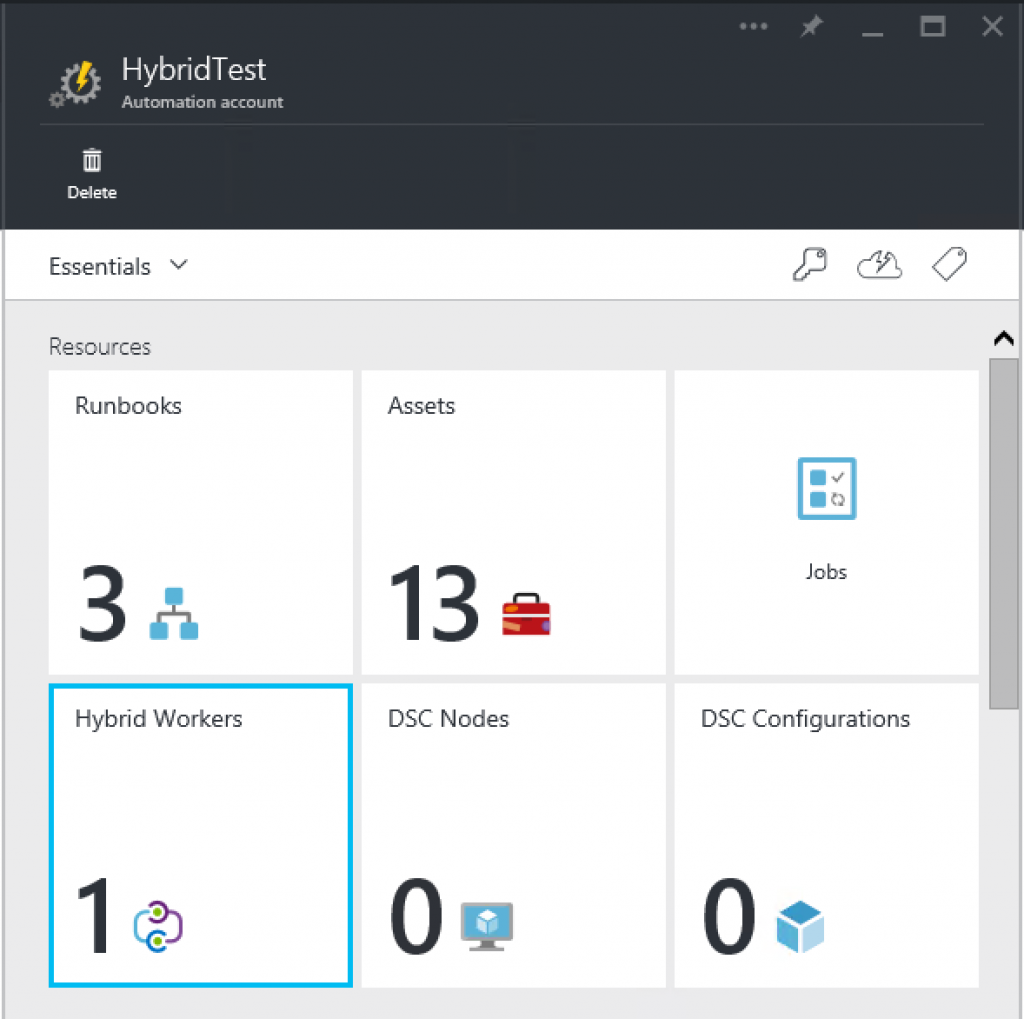
So how about the automation? I have already been using the automaton for different services within Azure but in this case I wanted to see how I could utilize the Hybrid worker and the VMware environment residing there.
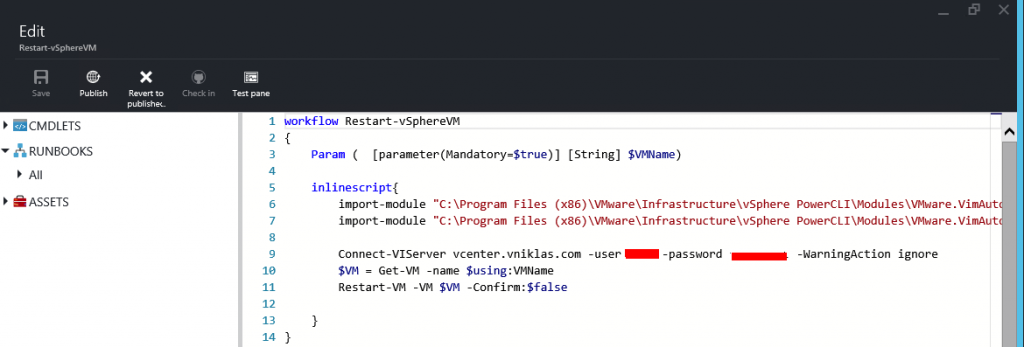
With the release of VMware PowerCLI 6 some of the stack are remade as PowerShell Modules.
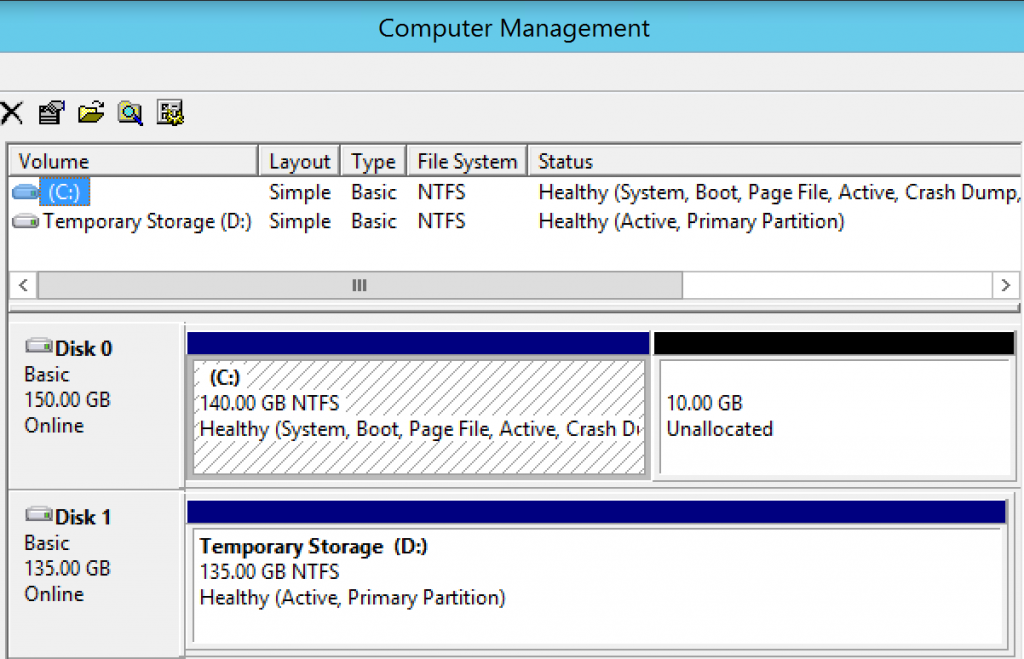
So if I configure a hybrid worker on premise with the PowerCLI installed I can then utilize that in a runbook that as an example takes an input variable VMName and restarts the VM (in this case I do it without being nice and asking for a shutdown but just pulling the plug)
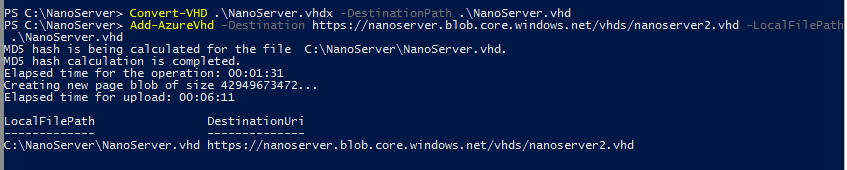
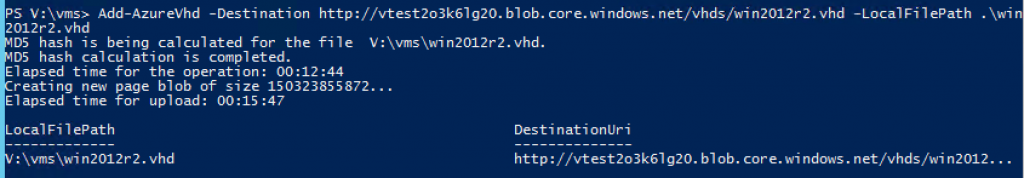
And here is the runbook:
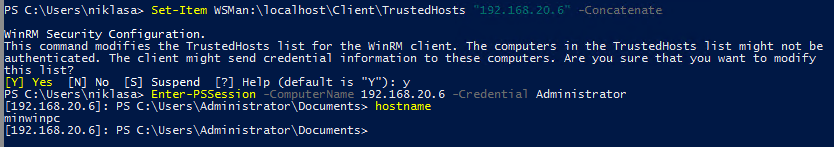
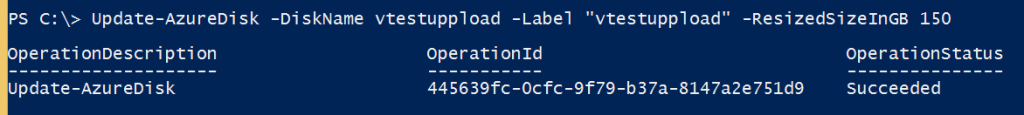
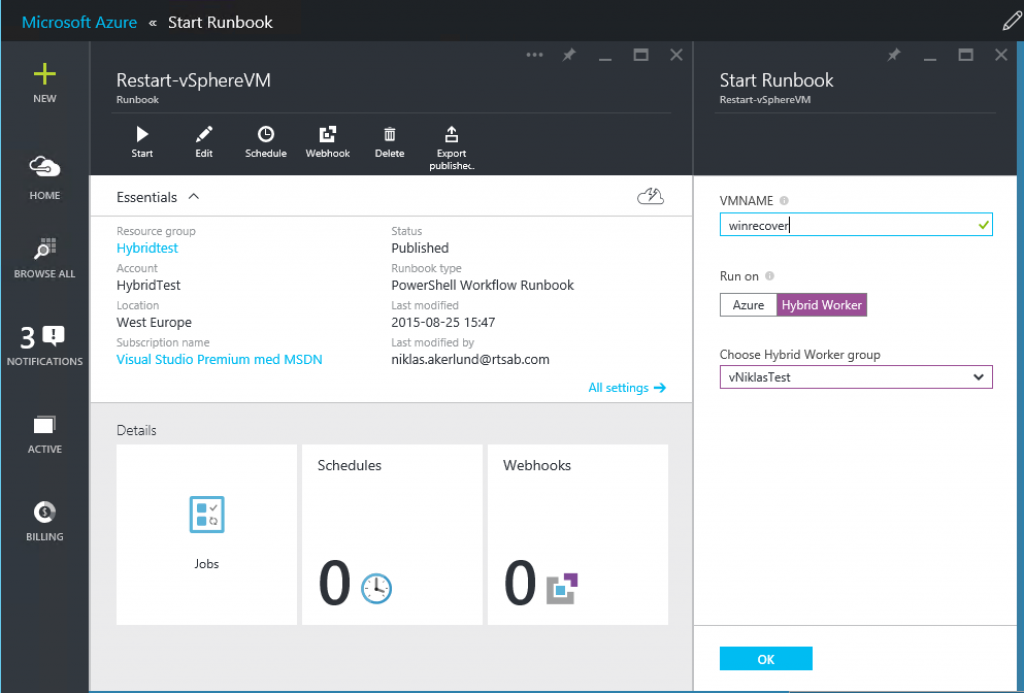
And here I start the runbook with the variable,
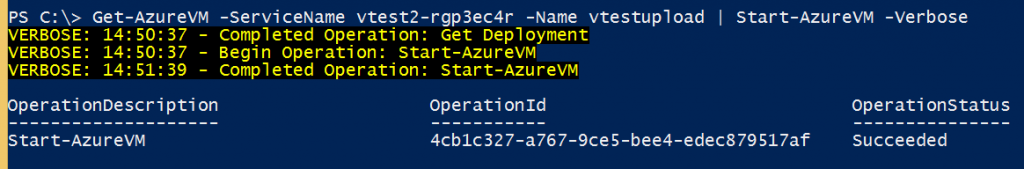
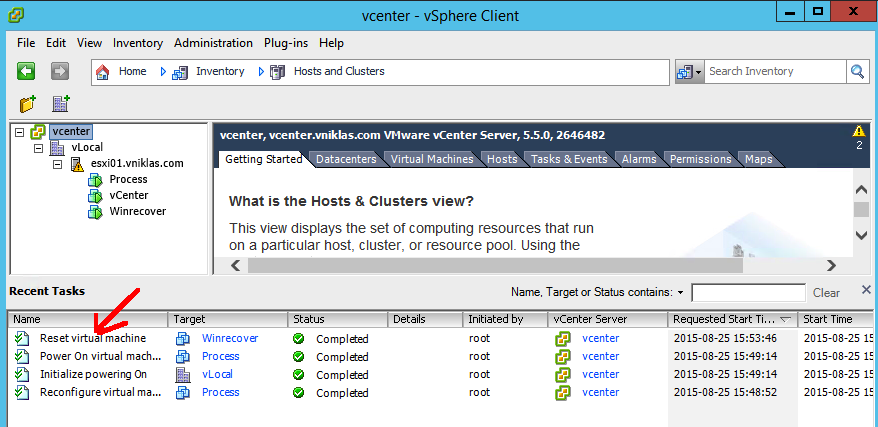
And as you can see in the vSphere Client my VM winrecover restarts
This can of course be made a bit more complex and also as you can see in the Azure automation view, scheduled. So if you have something that needs to be automated at 11 PM every night within your VMware vSphere environment it can be done by Azure Automation and Hybrid workers..