Windows Admin Center 1903
With the preview of Windows Admin Center 1903 that now is available in the insiders you now have some new extensions that make life even easier than before administering AD, DHCP and DNS.
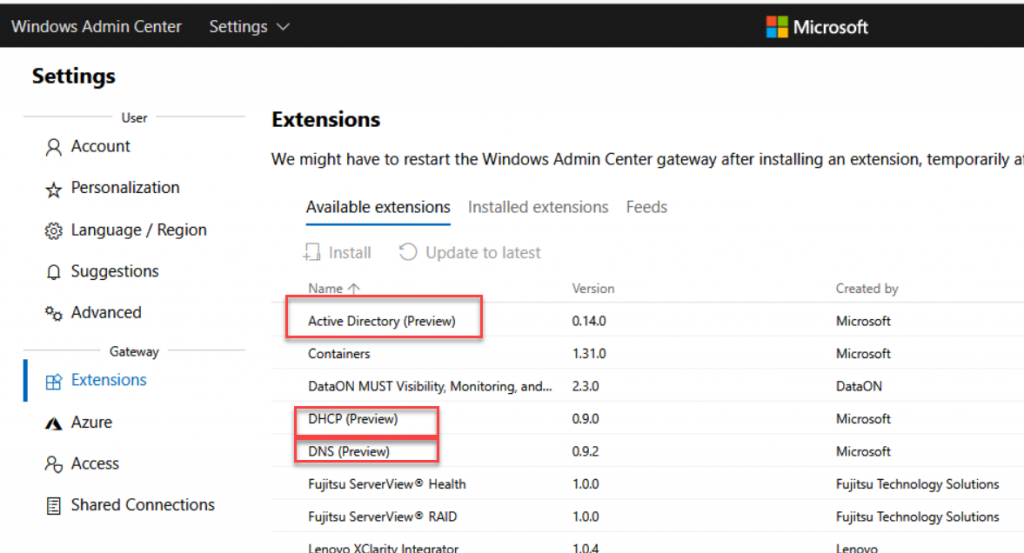
Once upgraded I go into the portal and there I find the new extensions.
And after installing them I can go to an domain controller and instantly administer user and computer objects
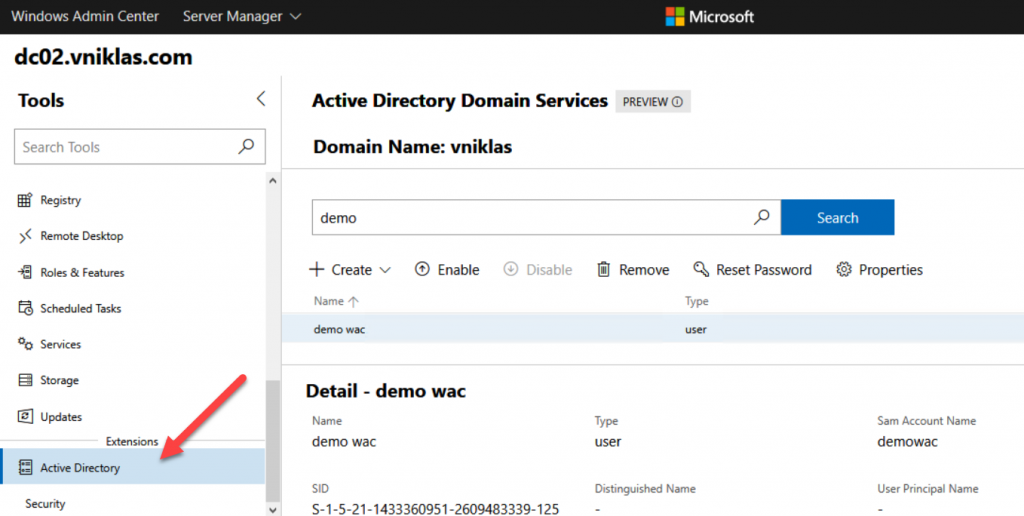
So please replace your old domain controllers and let go of the GUI option when you do it!
happy playing!